Why CISOs Can No Longer Afford to Wait for VMware
For more than two decades VMware was the safe bet. You could build on it, staff around it, and trust it to keep running.
Since Broadcom completed its $61 billion acquisition in late 2023, that trust has been eroding on every front. The pricing increases have grabbed the headlines, with customers reporting renewal hikes of 800 to 1,500%. But underneath the sticker shock is a more urgent concern: a growing list of critical security vulnerabilities, a support organization that struggles to keep pace, and a patching process that has left customers exposed for months.
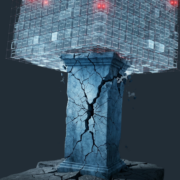
Your Hypervisor is a Top Target
With many organizations, the ESXi hypervisor is the foundation that every virtual machine in your environment sits on. If an attacker compromises it, they don’t just take down one system, but potentially hundreds or thousands of systems. In March 2025, Broadcom disclosed three zero-day vulnerabilities in ESXi attackers exploited before patches were available. The most critical carried a CVE severity score of 9.3 out of 10. When chained together, the three flaws allowed attackers to break out of a virtual machine, take control of the host, and move laterally across the environment. By early 2026, CISA confirmed attackers were actively using these vulnerabilities in ransomware campaigns.
Researchers at Huntress subsequently published analysis of a sophisticated exploit toolkit targeting 155 different ESXi configurations, with forensic evidence showing attackers built it more than a year before public disclosure. At the time, roughly 30,000 ESXi instances remained exposed on the public internet leaving many companies scrambling to patch.
These aren’t isolated events.
Additional critical advisories hit vCenter Server, VMware Cloud Foundation, and other portfolio products throughout 2025 and into 2026. Huntress data showed hypervisor-targeted ransomware incidents roughly quadrupled in the second half of 2025. In April 2025, a ransomware attack targeting Marks & Spencer’s ESXi environment caused an estimated $400 million in damages.
Broadcom is Nowhere to be Found When You Need Help Most
Fast-moving vulnerabilities demand fast-acting support. But the post-acquisition experience tells a different story.
Customers report longer response times, more escalation layers, and less technical depth with support engineers. Many smaller organizations say they can no longer reach VMware engineers directly and are routed through third-party distributors instead. What used to be a same-day conversation with a knowledgeable engineer has, for many, become a weeklong waiting game and ticking time bomb of frustration.
The most consequential failure, however, intersects with security teams trying to keep their heads above water with the volume of vulnerabilities in their environments. In mid-2025, multiple outlets reported that perpetual license holders without active Broadcom support contracts could not download security patches through the Broadcom portal. Broadcom’s own support staff acknowledged the issue, with some customers told patches could take up to 90 days to become available.
This occured despite a public commitment from Broadcom’s CEO to provide free access to critical security patches for supported vSphere versions. The situation was serious enough that a Dutch court ordered Broadcom to continue providing support to the Netherlands’ Ministry of Infrastructure after the agency declined a subscription model that would have increased costs by 85%.
Four Reasons Why Enough is Enough
Your security posture should never depend on your licensing status. When the ability to patch actively-exploited vulnerabilities is gated behind a portal that may or may not grant access based on your entitlement type, your licensing posture and your exposure window are directly linked. The documented 90-day patch delay for perpetual license holders is not abstract. It is a vendor-acknowledged gap in your ability to remediate known threats.
Degraded support directly extends your exposure window. When a critical advisory drops and your first call routes through a distributor, then to a generalist, then to a specialist who may not be available, your organization absorbs every hour of that delay as additional risk. Slower vendor response times translate directly into longer periods where your business sits exposed.
You need a plan with options, not just a plan to stay. This is not about abandoning VMware tomorrow. It is about making sure that staying is an active, informed choice rather than a default one. Organizations that have mapped out credible alternatives enter every renewal negotiation and every incident response from a position of strength. Those that have not are subject to whatever terms and timelines their vendor dictates.
Cloud migration deserves evaluation on its own merits. Public cloud does not eliminate security risk, and anyone who says otherwise is not being straight with you. What it does change is the operating and shared responsibility models. Cloud eliminates per-core licensing traps and forced bundling allowing organizations to focus on what actually matters, delivering applications and services to the business. It introduces its own complexity around cost governance, but the question worth asking is whether those tradeoffs are better than the ones you are making today?
Ready to Start the Conversation?
At In Balance IT Solutions, we help organizations chart a practical path to what we call VMware Freedom. Whether that means building a cloud migration roadmap, designing a hybrid architecture, or developing a contingency plan that gives your organization real leverage at the negotiating table, our cloud and security teams are ready to help.
Don’t wait for the next advisory or the next renewal shock to force your hand. Reach out to In Balance IT Solutions today.
Michael Caplan is the Chief Technology Officer for In Balance IT Solutions.